This is an old revision of the document!
Table of Contents
Users Authentication
SQL Database Authentication
coreBOS validates user access using a password hash saved in the database. The password can be changed by the user and also by users with administration rights. The password can be configured to automatically expire activating the scheduled task to do so.
This is the default behavior of the application called SQL mode, but there are various other ways of giving access to your users.
LDAP Authentication
Requirements
- coreBOS installed
- LDAP server should be installed and accessible by coreBOS.
- You will need to have php-ldap extension installed on your server.
Configuration
- Set the global variable User_AuthenticationType to LDAP for the user
- Configure the LDAP support in modules/Users/authTypes/config.ldap.php
Remember that LDAP is only for authorizing, the user must exist in both applications.
Query
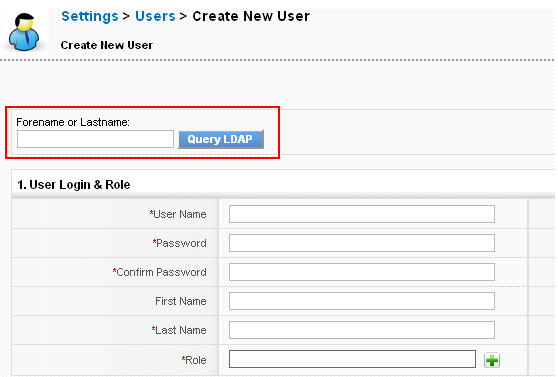
If the default User_AuthenticationType is set to LDAP or AD (Active Directory), then on the create user screen you will have a Query Button.
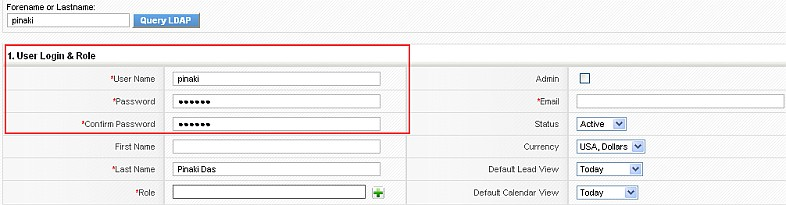
Enter the LDAP username you would like to query and click on the “Query LDAP” button. This will retrieve the users information from LDAP and automatically fill up the user fields.
Fill up any missing mandatory fields and click on the save button to create the user. Once created, you can log in using the username and LDAP password. The password for the user will be picked from LDAP which means that changes in LDAP password would reflect in the application without any changes.
Active Directory Authentication
Configuration
adLDAP is configured directly in the adLDAP.php class (ugh!). Just open and customize the settings for your needs. The following settings match those needed for a 2012R2 Active Directory.
...
class adLDAP {
/**
* Define the different types of account in AD
*/
const ADLDAP_NORMAL_ACCOUNT = 805306368;
const ADLDAP_WORKSTATION_TRUST = 805306369;
const ADLDAP_INTERDOMAIN_TRUST = 805306370;
const ADLDAP_SECURITY_GLOBAL_GROUP = 268435456;
const ADLDAP_DISTRIBUTION_GROUP = 268435457;
const ADLDAP_SECURITY_LOCAL_GROUP = 536870912;
const ADLDAP_DISTRIBUTION_LOCAL_GROUP = 536870913;
const ADLDAP_FOLDER = 'OU';
const ADLDAP_CONTAINER = 'CN';
/**
* The default port for LDAP non-SSL connections
*/
const ADLDAP_LDAP_PORT = '389';
/**
* The default port for LDAPS SSL connections
*/
const ADLDAP_LDAPS_PORT = '636';
/**
* The account suffix for your domain, can be set when the class is invoked
*
* @var string
*/
protected $accountSuffix = "@cortoso.com";
/**
* The base dn for your domain
*
* If this is set to null then adLDAP will attempt to obtain this automatically from the rootDSE
*
* @var string
*/
protected $baseDn = "";
/**
* Port used to talk to the domain controllers.
*
* @var int
*/
protected $adPort = self::ADLDAP_LDAP_PORT;
/**
* Array of domain controllers. Specifiy multiple controllers if you
* would like the class to balance the LDAP queries amongst multiple servers
*
* @var array
*/
protected $domainControllers = array("dc01.cortoso.com", "dc02.cortoso.com");
/**
* Optional account with higher privileges for searching
* This should be set to a domain admin account
*
* @var string
* @var string
*/
protected $adminUsername = "ldap-binduser";
protected $adminPassword = "super-password";
/**
* AD does not return the primary group. http://support.microsoft.com/?kbid=321360
* This tweak will resolve the real primary group.
* Setting to false will fudge "Domain Users" and is much faster. Keep in mind though that if
* someone's primary group is NOT domain users, this is obviously going to mess up the results
*
* @var bool
*/
protected $realPrimaryGroup = false;
/**
* Use SSL (LDAPS), your server needs to be setup, please see
* http://adldap.sourceforge.net/wiki/doku.php?id=ldap_over_ssl
*
* @var bool
*/
protected $useSSL = false;
/**
* Use TLS
* If you wish to use TLS you should ensure that $useSSL is set to false and vice-versa
*
* @var bool
*/
protected $useTLS = true;
/**
* Use SSO
* To indicate to adLDAP to reuse password set by the brower through NTLM or Kerberos
*
* @var bool
*/
protected $useSSO = false;
/**
* When querying group memberships, do it recursively
* eg. User Fred is a member of Group A, which is a member of Group B, which is a member of Group C
* user_ingroup("Fred","C") will returns true with this option turned on, false if turned off
*
* @var bool
*/
protected $recursiveGroups = true;
...
?>
- configure multiple domain-controllers to prevent SPOFs
- configured hostnames for your domain-controllers and common names in their SSL certificates have to match to prevent SSL trust errors
- use TLS to ensure encrypted transport of user account data
- create a special user for ldap binding, without any further permissions and with unlimited password validity (configure it in adLDAP with AdminUsername and AdminPassword parameters)
OpenLDAP Authentication
Notes and comments
- All admin users will always authenticate in SQL mode (against the database)
- You can set the authentication variable to any value for any user, effectively authenticating each one using different methods
- Make sure the case for the user names match that of your coreBOS usernames
- You cannot have spaces or special characters in the LDAP username as these are not supported by coreBOS.